Cybersecurity
The cybersecurity guidelines were defined as a guide to address the current challenges of the discipline in strategic planning, so that these activities are analyzed, matured or gradually adopted in the government and management of their institutions.
Guidelines
Financial services through digital means continue to expand, demanding new technologies and a growing interconnection between those who participate in the financial system.
This context presents challenges to the entire financial ecosystem, whether or not they are regulated by the Central Bank, such as financial institutions, network operators, clearing houses, third-party service providers, Fintechs, among others. Therefore, it is essential to have a plan that addresses the new risks associated with this digital expansion.
The following guidelines aim to accompany the establishment and incorporation of cybersecurity and cyber resilience into the strategic planning of each organization:
Cybersecurity Framework and Strategy
The purpose of having a strategy and a framework of reference is to guide how to effectively identify, manage, and reduce cyber risks in an integrated manner. Financial institutions, third parties and the entire financial sector should establish strategies and adopt a cybersecurity framework according to their size, complexity, risk profile and culture, taking into account current threats and vulnerabilities.
Government
Strategy is the responsibility of the governance of the organization. It is necessary to have clearly defined structures, roles and functions to deal with this problem, as well as to have the forecasts in each project. In addition, to promote communication between the business units, the different areas of information technology, the risk areas, the fraud areas and those areas whose activities are related to control in accordance with their missions and functions.
Evaluation of controls and risk
Analyze the risk presented by the people, processes, technology, and underlying data in relation to the entity itself and also evaluate the risks of an entity based on its functions, activities, channels, products, and services. Control evaluations must consider the cyber risks that the entity represents or faces for the ecosystem it is part of, such as service providers, government agencies, users of financial services and other organizations with which it interacts.
Monitoring
The monitoring process should provide support to maintain the risk levels defined as acceptable by the organization’s management and allow for the improvement or remedying of the corresponding weaknesses. Testing protocols, cyber exercises, and audits are essential. Depending on the nature of an entity or organization, its control environment, and risk profile, the testing and auditing functions of the controls should be appropriately independent of the personnel responsible for implementing the cybersecurity program.
Reply
As part of their risk and control assessments, entities should implement incident response processes and other controls to facilitate a timely and appropriate response. These controls should clearly address responsibilities in decision-making, define escalation procedures, and establish processes for communicating with internal and external communities of interest. Exercises and the adoption of internal protocols and among entities or organizations in the ecosystem are promoted. The exercises also allow institutions and authorities to identify situations that could affect the ability of those involved to maintain an acceptable level of service, critical functions and activities, and other activities that may be relevant to the financial system.
Recovery
Once operational stability and integrity are ensured, the rapid and effective recovery of operations should be based on the prioritization of critical processes and in accordance with the objectives set by the responsible authorities of the entity or organization. Financial sector confidence is significantly improved when entities or organizations and authorities have the ability to assist each other in the resumption and recovery of critical functions, processes, and activities. Establishing and testing contingency plans for essential activities and processes can contribute to a faster and more effective recovery.
Sharing information
Sharing technical information, such as threat indicators or modalities on how vulnerabilities were exploited, or fraud modalities, allows entities to stay up to date on their defenses and learn about the methods that are being used most. This practice facilitates a collective understanding of how vulnerabilities that affect the entire sector, critical economic functions and even jeopardize financial stability can be exploited. Given its importance, responsible entities, organizations and authorities will work to identify and address impediments to information sharing.
Continuous learning
Threats and vulnerabilities in the cyber ecosystem evolve rapidly, as do best practices and technical standards. The composition of the financial sector also changes over time, as new products and services emerge, and third-party service providers are increasingly relied upon. Cybersecurity strategies and frameworks need to be regularly reviewed and updated to adapt to changes in the control environment and threats, improve user awareness, and deploy resources effectively.
For implementation, particular characteristics, risk profiles, and business impact analysis (BIA) must be considered as appropriate. It is expected that these guidelines will be adopted by all those regulated by the Central Bank in the construction of a financial ecosystem committed to cybersecurity.
In addition to the principles, the Cybersecurity Glossary is published. A tool that establishes definitions so that all people from the different disciplines involved in cybersecurity processes have a common language.
Self-Diagnostic Guide
The following questionnaire has been developed to help identify the current state of your organization with respect to the Cybersecurity Guidelines.
The organization that wishes to do so can answer these questions and obtain a self-diagnosis on the degree of adoption of the defined principles.
1. Does the organization take into account the established Cybersecurity and Cyber Resilience Guidelines?
1.1. Do you have a cybersecurity strategy tailored to your particular characteristics, risk profile, and business impact analysis?
1.2. Do you use a framework for cybersecurity management and cyber resilience?
1.3. Do you have adequate organizational structures, roles, and functions to implement the Guidelines?
1.4. Does cybersecurity participate in all of the organization’s projects from the beginning?
1.5. Do you have a methodology for managing cyber risk integrated into corporate risk that includes all relevant controls in place?
1.6. Do you implement continuous cyber risk monitoring?
1.7. Has a Cyber Incident Response Plan that causes a disruptive event in the organization been properly defined, implemented and tested?
1.8. Have you discussed or evaluated the advantages and disadvantages of sharing information on cyber incidents and cyber threats or fraud modalities? Have you initiated actions to share information?
2. Do you take cybersecurity criteria into account in your decision-making?
2.1. Do you incorporate cyber risk management by design, for new products and services?
2.2. Are cybersecurity aspects considered when evaluating the effectiveness of business operations and existing infrastructure? Does it also include IT infrastructures or services provided by third parties?
2.3. Does senior management or at the strategic level oversee the design, implementation, and effectiveness of cybersecurity programs?
2.4. Does the Board or senior management receive reports of threats or serious cyber incidents from your industry periodically in order to make informed decisions in both the short and medium term?
2.5. Do threat and vulnerability reports influence the definition of the organization’s risk appetite?
3. Are you aware that a disruption is highly likely?
3.1. Considering that implementing layered detection and prevention controls reduces the likelihood of incidents, do you implement layered security?
3.2. Nowadays we know that a completely secure environment cannot be guaranteed, so it is assumed that certain incidents will occur, who makes the decisions, do they understand that the allocation of resources must be aligned with the cybersecurity strategy?
3.3. Are the Cyber Incident Response Plan comprehensive tests carried out?
3.4. Do Incident Response plans integrate with Business Continuity Plans?
3.5. Is the Business Continuity Plan aligned with the priorities established in the Business Impact Analysis?
4. Does it adapt to the vulnerabilities and threats that arise all the time? Do you take an adaptive approach to cybersecurity?
4.1. Are cyber-exercises promoted at the entity, industry or cross-sector level?
4.2. Do you prepare for crises (unexpected situations), planning possible scenarios and thinking about containment and recovery?
4.3. Is a learning and continuous improvement approach promoted as part of the cybersecurity strategy?
5. Do you build a culture of cybersecurity?
5.1. Do you develop an ongoing program so that cybersecurity skills, capabilities, and behaviors are internalized for everyone in the organization?
5.2. Are the awareness of all personnel and cybersecurity considered in the processes at the same level as technological solutions? Is it reflected in investment decisions?
5.3. Are cybersecurity training and awareness programs equally aimed at users, employees and senior management?
5.4. Keeping in mind that effective cybersecurity is based on involving and educating people. Are the necessary campaigns carried out? Is progress measured?
5.5. Is the cybersecurity training and awareness strategy developed with the aim of transforming the paradigm known as: “people are the weakest link” into the new paradigm “people are the most valuable asset“?
Regulation
Cyber incidents
Communication A 7266, Guidelines for response and recovery to cyber incidents (RRCI) and Communication A 8280, Adaptations.
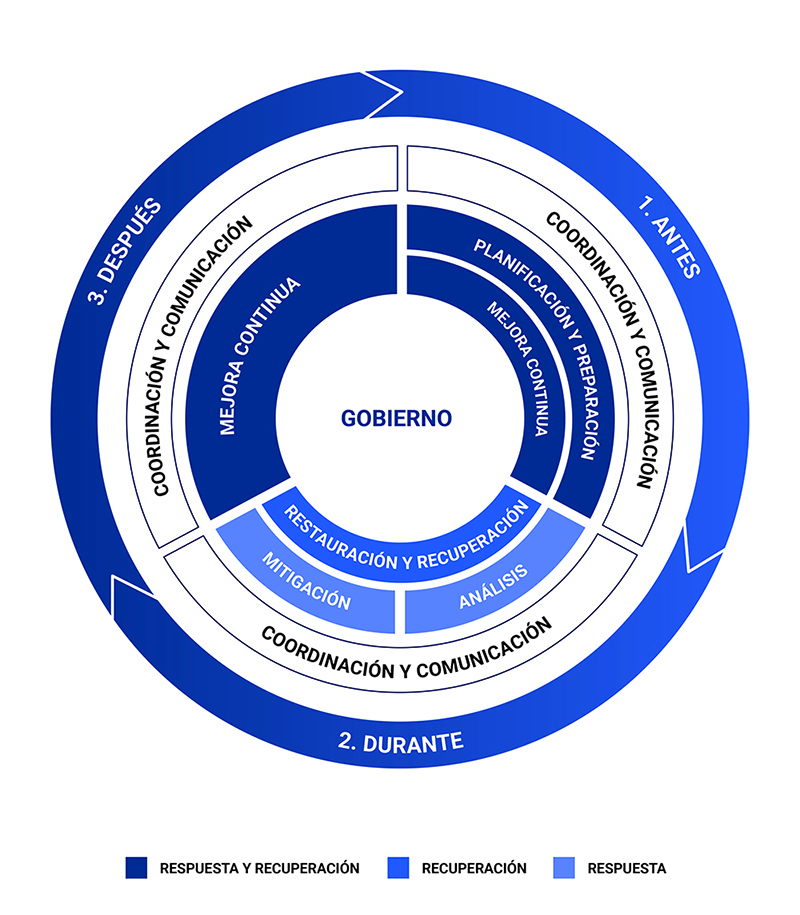
The Central Bank of the Argentine Republic established a series of guidelines for response and recovery from cyber incidents in order to limit risks to financial stability and promote the cyber resilience of the ecosystem as a whole, in line with the recommendations of the Financial Stability Board (FSB) included in the work Effective practices for response and recovery from cyber incidents, Final Report.
These guidelines are aimed at Financial Institutions, Payment Service Providers (PSPs) included in the BCRA’s PSP Registry and Financial Market Infrastructures known as systemically important payment systems. However, due to their general nature, they can also be adopted by any institution in the financial system, providers of information and communication technology services, among others.
A cyber incident, according to the definition included in the glossary published on the BCRA website, is an event related to a technological infrastructure in which people, processes, data and information systems interact and that endangers cybersecurity or violates security policies, security procedures or policies of use acceptable by entities. whether or not that event is the product of malicious activity.
Regarding the implementation of these guidelines, the actors covered will be able to adopt the practices that are most appropriate for their business models, taking into account their size, complexity or risks in relation to the financial ecosystem. They must record the basis for the implementation criteria adopted, which must be made available to the Superintendence of Financial and Exchange Entities, when requested.
The guidelines contemplated in communications A 7266 and A 8280 are as follows:
Government
Here the definition of a framework for decision-making is promoted, where the necessary roles and responsibilities are assigned for the coordination of these activities in such a way that the necessary internal and external participants are involved when a cyber incident occurs. The scheme through which response and recovery activities are organized and managed is proposed, a culture that accepts the eventual occurrence of cyber incidents, faces them and manages them appropriately is promoted.
Planning and preparation
This item contemplates the preparation prior to the occurrence of an incident that plays a significant role in the effectiveness of response and recovery activities. This guideline focuses on establishing and maintaining the organization’s planning and preparedness capabilities, which will allow it to respond to, recover from, and restore critical activities, systems, and data compromised in a cyber incident until normal operation returns. In this section, plans and procedures play an important role, which must include the necessary criteria to know when to activate the measures and how to respond to cyber incidents.
Analyses
This guideline refers to forensic analysis, the determination of criticality and impact of the cyber incident and the investigation of the cause that originated it. The need to define a taxonomy to classify cyber incidents is highlighted.
Mitigation
This axis focuses on mitigation measures in order to prevent the aggravation of the situation and eradicate or eliminate the consequences of incidents in a timely manner, to minimize their impact on operations and services. It contemplates containment, isolation and eradication measures that are of great importance.
Restoration and recovery
These guidelines cover the activities that must be performed to restore systems and assets affected by a cyber incident, and recover affected data, operations, and services to their usual state, in a secure manner.
Coordination and communication
This section refers to the adequate coordination of the organization with the different actors involved, both internal and external, and with the authorities. During the lifecycle of a cyber incident, stakeholders must be coordinated to provide a common response and attention to threats to improve the cyber resilience of the system. The importance of defining the language and the necessary frequency of communication is highlighted, according to the type of target audience.
Continuous improvement
Finally, this guideline refers to the processes that must be considered to improve cyber incident response and recovery activities and capabilities, through the lessons learned in case resolution and the use of proactive tools, in particular the performance of exercises, tests and drills.
Cyber incident notification
Cyber incidents defined as critical and important must be reported to the External Systems Audit Management of the SEFyC. Those incidents that affect at least:
- The normal provision of services provided to clients by any means.
- The execution of transactions that must be carried out in a certain time slot.
- The exchange of information with other obligated entities and their associated service providers in relation to the operations of customers.
- Data to customer information for loss or unauthorized or fraudulent disclosure.
Incidents originating in third parties and in their entire chain of providers that are linked to the obligated entities must also be notified when they affect the availability for the normal provision of services to customers, or put at risk the integrity and confidentiality of the information.
 Risks related to Information Technology and Security.
Risks related to Information Technology and Security.
Communication A 7724 of “Minimum requirements for the management and control of technology and information security risks” contains the governance, organizational, and technical guidelines to be considered to carry out the management and control mentioned in the organization.
Its structure is as follows:
Section 1. General provisions.
Section 2. Technology and information security governance.
Section 3: Information Security and Technology Risk Management.
Section 4: Information Technology Management.
Section 5: Information Security Management.
Section 6: Business Continuity Management.
Section 7. Technological infrastructure and processing.
Section 8: Cyber incident management.
Section 9: Software Development, Acquisition, and Maintenance.
Section 10: Managing the Relationship with Third Parties.
Section 11: Electronic channels.
Glossary
This glossary is a tool that establishes definitions so that all people from the different disciplines involved in cybersecurity processes have a common language.
Its purpose is to bring together criteria and definitions among cybersecurity experts from different jurisdictions and to maximize the interdisciplinary work required to protect the financial system as a whole.
In an interconnected society and increasingly digital in the consumption of services, the need to interact between different disciplines and with other jurisdictions becomes intrinsically necessary, for this reason having a set of common terms helps to better understand cybersecurity problems.
The terms and definitions in the glossary were developed to be used only with respect to the financial services sector and financial institutions and are not intended to be used for a legal interpretation of any international agreement or contracts between private parties.
Notes
The citations from the sources below have been abbreviated. The full citation can be found at the end of the glossary.
Terms defined in the glossary are italicized when used in glossary definitions.
In the glossary, the term “entity” includes human persons when the context requires it.
Asset
A resource of tangible or intangible value that should be protected, including people, information, infrastructure, finance, and reputation.
Source: ISACA Fundamentals.
Threat actor
A person, group, or organization that is allegedly operating with malicious intent.
Source: Adapted from STIX.
Advanced Persistent Threat (APT)
A threat actor who has sophisticated levels of knowledge and significant resources that enable them to generate opportunities to achieve their objectives using numerous threat vectors. Advanced persistent threat: (i) pursues its objectives repeatedly over an extended period of time; (ii) it adapts to the efforts made by those who defend themselves against it in an attempt to resist it; and (iii) is determined to carry out its objectives.
Source: Adapted from NIST.
Vulnerability assessment
Systematic review of an information system, along with its controls and processes, to determine the adequacy of security measures, identify security deficiencies, provide data from which to predict the effectiveness of proposed security measures, and confirm the adequacy of those measures after implementation.
Source: Adapted from NIST.
Multi-factor authentication
Using two or more of the following factors to verify a user’s identity: knowledge factor, “something a person knows”; possession factor, “something that a person has”; biometric factor, “a biological or behavioral characteristic of a person.”
Source: Adapted from ISO/IEC 27040:2015 and ISO/IEC 2832-37:2017 (definition of “biometric characteristic”).
Authenticity
Property that consists of an entity being what it claims to be.
Source: ISO/IEC 27000:2018.
Cyber advisory
Notification of new trends or developments about a cyber threat against information systems or about a vulnerability in information systems. Such notification may include an analytical study of trends, intentions, technologies, or tactics employed to attack information systems.
Source: Adapted from NIST.
Campaign
A set of coordinated adverse behaviors that describes a series of malicious activities against one or more specific targets over a period of time.
Source: Adapted from STIX.
Cyber- or cyber
Relating to an interconnected technological infrastructure in which people, processes, data and information systems interact.
Source: Adapted from CPMI-IOSCO (citation from NICCS).
Cyber alertNotification of a specific cyber incident or that a cyber threat has been directed against an organization’s information systems.
Source: Adapted from NIST.
Cyber threat
A circumstance that could exploit one or more vulnerabilities and affect cybersecurity.
Source: Adapted from CPMI-IOSCO.
Cyber incident
Cyber event that: i. jeopardizes the cybersecurity of an information system or the information that the system processes, stores or transmits; or ii. violates security policies, security procedures, or acceptable use policies, whether or not it is the result of malicious activity.
Source: Adapted from NIST (definition of “incident”).
Cyber resilience
An organization’s ability to continue to carry out its mission by anticipating and adapting to cyber threats and other relevant changes in the environment, and by resisting, containing, and recovering quickly from cyber incidents.
Source: Adapted from CERT Glossary (definition of “operational resilience”), CPMI-IOSCO, and NIST (definition of “resilience”).
Cybersecurity
Preservation of the confidentiality, integrity and availability of information and/or information systems through the cybernetic medium. Other properties may also be involved, such as authenticity, traceability, non-repudiation, and reliability.
Source: Adapted from ISO/IEC 27032:2012.
Compromise
Transgression of the security of an information system.
Source: Adapted from ISO 21188:2018.
Reliability
Uniformity in behavior and desired outcomes.
Source: ISO/IEC 27000:2018.
Confidentiality
Ownership under which information is not available to unauthorized persons, entities, processes, or systems, nor is it disclosed to unauthorized persons, entities, processes, or systems.
Source: Adapted from ISO/IEC 27000:2018.
Access control
Means of ensuring that access to assets is authorized and restricted based on business and security-related requirements.
Source: ISO/IEC 27000:2018.
Course of Action (CoA)
One or more actions that are taken to prevent or respond to a cyber incident. This concept can refer to automatable technical responses, but it can also describe other actions, such as employee training or policy changes.
Source: Adapted from STIX.
Defence-in-depth
Security strategy that encompasses people, processes, and technology to establish a series of barriers at multiple levels and dimensions of the organization.
Source: Adapted from NIST and FFIEC.
Denial of Service (DoS)
Action to prevent authorized access to information or information systems, or to delay the execution of operations and functions of information systems, which entails the loss of availability for authorized users.
Source: Adapted from ISO/IEC 27033-1:2015.
Distributed Denial of Service (DDoS)
Denial of service that is carried out using numerous sources simultaneously.
Source: Adapted from NICCS.
Detect (function) (detect)
Develop and implement appropriate activities to identify a cyber event.
Source: Adapted from NIST Framework.
Availability
Accessible and usable on demand by an authorized entity.
Source: ISO/IEC 27000:2018.
Incident Response Team (IRT) [also known as CERT or CSIRT]
A team made up of trained and reliable members of the organization that handles incidents throughout their life cycle.
Source: ISO/IEC 27035-1:2016.
Threat assessment
Process of formal assessment of the degree of threat to an organization and description of the nature of the threat.
Source: Adapted from NIST.
Cyber event
Observable occurrence in an information system. Cyber events sometimes indicate that a cyber incident is occurring.
Source: Adapted from NIST (definition of “event”).
Exploit
A defined way of transgressing the security of information systems through a vulnerability.
Source: ISO/IEC 27039:2015.
Identity and Access Management (IAM)
It comprises people, processes, and technology to identify and manage the data used in an information system to authenticate users and grant or deny access rights to data and system resources.
Source: Adapted from ISACA Full Glossary.
Patch management
Systematic reporting, identifying, deploying, installing, and verifying patches of operating systems and application software codes. These hotfixes are known as “patches,” “hot fixes,” and “service packs.”
Source: NIST.
Identify (function) (identify)
Develop the organizational understanding necessary to manage the cyber risk to which assets and capabilities are exposed.
Source: Adapted from NIST Framework.
Data breach
An undertaking that accidentally or unlawfully results in the destruction, loss, alteration, or unauthorized disclosure of or access to data transmitted, stored, or otherwise processed.
Source: Adapted from ISO/IEC 27040:2015.
Indicators of Compromise (IoCs)
Signs that indicate that a cyber incident could have occurred or could be occurring.
Source: Adapted from NIST (definition of “indicator”).
Social engineering
A general term that describes the action of trying to deceive people into revealing information or performing certain actions.
Source: Adapted from FFIEC.
Integrity
Quality of accuracy and completeness.
Source: ISO/IEC 27000:2018.
Threat intelligence
Threat information that has been aggregated, transformed, analyzed, interpreted, or enriched to provide the context needed for decision-making processes.
Source: NIST 800-150.
Information sharing
The action of sharing data, information and/or knowledge that can be used to manage risks or respond to events.
Source: Adapted from NICCS.
Malware
Software designed with a malicious purpose and containing features or capabilities that could cause direct or indirect harm to entities or their information systems.
Source: Adapted from ISO/IEC 27032:2012.
Non-repudiation
Ability to demonstrate the occurrence of an event or action and the entities that originated them.
Source: ISO 27000:2018.
Cyber incident response plan
Documentation of a predetermined set of instructions or procedures for responding to a cyber incident and limiting its consequences.
Source: Adapted from NIST (definition of “incident response plan”) and NICCS.
Protect
Develop and implement the appropriate safeguards to guarantee the provision of services and limit or contain the impact of cyber incidents.
Source: Adapted from NIST Framework.
Traffic Light Protocol (TLP)
A set of designations used to ensure that information is shared only with defined recipients. It uses a pre-established color code (traffic light) to indicate the expected exchange limits to be applied by the receiver.
Source: Adapted from FIRST.
Recover
Develop and implement appropriate activities to maintain cyber resilience plans and restore capabilities or services that have been affected due to a cyber incident.
Source: Adapted from NIST Framework.
Reply (function) (respond)
Develop and implement appropriate activities to take action on a detected cyber event.
Source: Adapted from NIST Framework.
Cyber risk
Combination of the likelihood of cyber incidents occurring and their impact. Source: Adapted from CPMI-IOSCO, ISACA Fundamentals (definition of “risk”) and ISACA Full Glossary (definition of “risk”).
Information system
A set of applications, services, information technology assets, or other information management components, including the operating environment.
Source: Adapted from ISO/IEC 27000:2018.
Tactics, Techniques and Procedures (TTPs)
Behavior of a threat actor. A tactic is the highest-level description of this behavior, while techniques provide a more detailed description of behavior in the context of a tactic and procedures involve a lower-level, highly detailed description in the context of a technique.
Source: Adapted from NIST 800-150.
Penetration testing
A testing methodology in which testers, using all available documentation (e.g., system design, source code, manuals) and working with specific constraints, attempt to circumvent the security functions of an information system.
Source: NIST.
Threat-Led Penetration Testing (TLPT) [also known as red team testing]
A controlled attempt to compromise an entity’s cyber resilience by simulating the tactics, techniques, and procedures of real threat actors. It is based on targeted threat intelligence and focuses on an entity’s people, processes, and technology, with minimal prior knowledge and impact on operations.
Source: G-7 – Fundamental Elements
Accountability
Ownership that ensures that an entity’s actions can be unambiguously traced and attributed to that entity.
Source: ISO/IEC 2382:2015.
Threat vector
A path or route used by the threat actor to gain access to the target. Source: Adapted from ISACA Fundamentals. Verification Confirmation, through the provision of objective evidence, that specified requirements have been met.
Source: ISO/IEC 27042:2015.
Vulnerability
Weakness, susceptibility, or defect of an asset or control that can be exploited by one or more threats.
Source: Adapted from CPMI-IOSCO and ISO/IEC 27000:2018.
Queries
Write to normas.segtecinf@bcra.gob.ar
Recent Comments